China’s onslaught of cyberattacks on essential infrastructure is probably going a contingency transfer designed to realize a strategic benefit within the occasion of kinetic warfare, in line with the US Division of Protection (DoD).
The company’s 2023 Cyber Strategy released this week flagged an uptick in state-sponsored cybercrime from the Folks’s Republic of China (PRC), particularly in opposition to delicate targets that might affect navy response, so as “to counter US standard navy energy and degrade the fight functionality of the Joint Drive.”
The DoD alleged within the report that the PRC “poses a broad and pervasive cyberespionage risk,” surveilling people past its borders, stealing expertise secrets and techniques, and undermining military-industrial complicated capabilities. However the exercise goes past run-of-the-mill intelligence-gathering, the company warned.
“This malicious cyber exercise informs the PRC’s preparations for struggle,” in line with the report. “Within the occasion of battle, the PRC doubtless intends to launch harmful cyberattacks in opposition to the US Homeland with a view to hinder navy mobilization, sow chaos, and divert consideration and sources. It can additionally doubtless search to disrupt key networks which allow Joint Drive energy projection in fight.”
An Rising Chinese language Give attention to Army Degradation
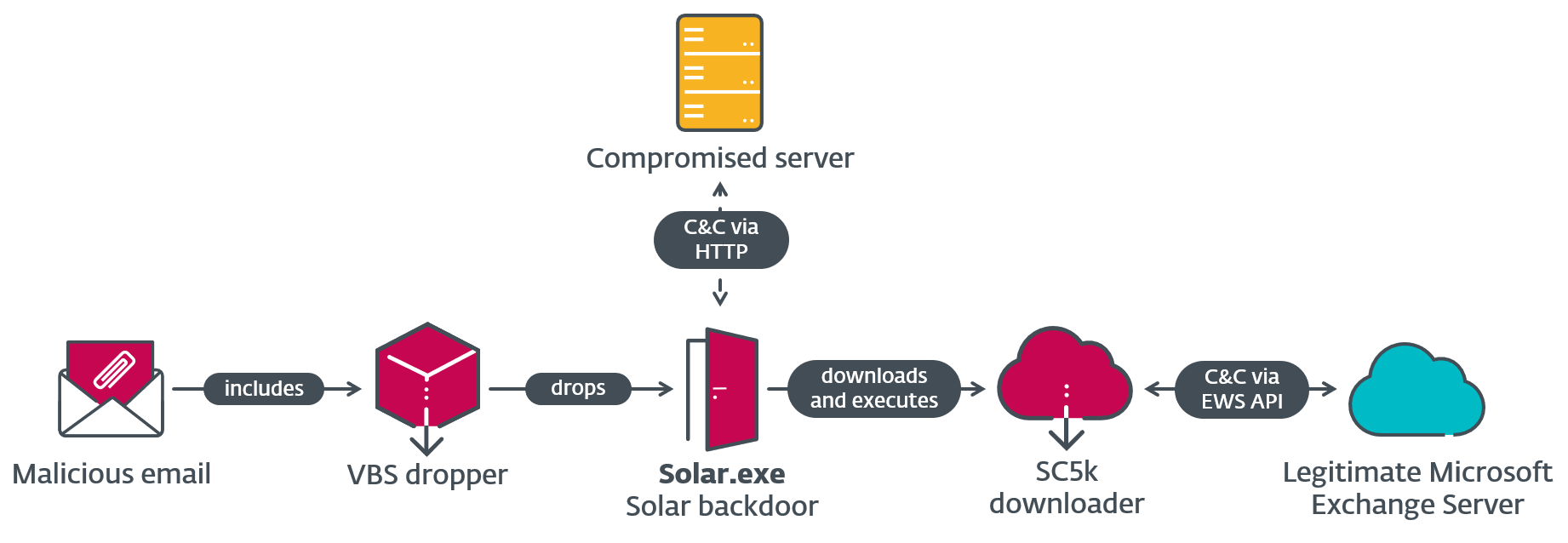
The concept cyber exercise may presage navy motion echoes assessments by Microsoft and others, made earlier this 12 months across the Volt Hurricane assaults. The Beijing-supported superior persistent risk (APT) made nationwide headlines within the US in Could, June, and July with a sequence of compromises that focused telecom networks; energy and water controls; US navy bases at residence and overseas; and different infrastructure whose disruption would hamper real-world navy operations.
Thus far, these compromises haven’t affected the operational expertise (OT) utilized by the victims, however talking at Black Hat USA in August, CISA Director Jen Easterly warned that the Chinese language authorities is probably going getting itself into the place to conduct disruptive assaults on American pipelines, railroads, and different essential infrastructure if the US will get concerned throughout a possible invasion of Taiwan.
“This APT strikes laterally into environments, having access to areas through which it would not historically reside,” says Blake Benson, cyber lead at ABS Group Consulting. “Moreover, this risk actor labored laborious to cowl their tracks by meticulously dumping all extracted reminiscence and artifacts, making it troublesome for safety groups to pinpoint the extent of infiltration.”
There could possibly be a kind of anti-halo impact at work too, on condition that military-focused assaults are prone to trigger collateral harm to bystander companies, in line with John Gallagher, vp of Viakoo Labs at Viakoo.
“Just about all exploits launched by nation-states ‘leak’ over to non-nation-state risk actors,” he warns. “Meaning organizations who rely upon IoT/OT methods might be direct targets in some unspecified time in the future to the identical threats being launched in opposition to nationwide essential infrastructure.”
Defending the Cyberwarfare House
To fight the exercise of Volt Hurricane and different threats to bodily security within the essential infrastructure area, the DoD laid out a “whole-of-government” effort in its report, designed to “enhance resilience and make it harder for adversaries to disrupt important companies.”
Dovetailing with the 2023 Nationwide Cybersecurity Technique, the DoD stated that it’s going to leverage “all legally accessible contractual mechanisms, sources, and operational preparations to enhance the cybersecurity of US essential infrastructure methods” and increase public-private partnerships. To that finish, it laid out a number of pages of hardening and readiness actions in its report.
An instance of a easy manner that the federal government can swing into preemptive motion is the transfer by CISA to supply free network security and vulnerability scanning to water utilities (PDF) to assist establish avenues of exploitation and shield them in opposition to cyberattacks.
“When it comes to nationwide protection there was a decades-long evolution within the quantity, velocity, and persistence of cyber threats, which is tied to each the elevated computational capabilities of IoT/OT and important infrastructure, in addition to elevated sophistication by nation-state risk actors,” Gallagher warns. “From Stuxnet by way of Volt Hurricane to the present struggle between Ukraine and Russia (the place each side have exploited susceptible IoT/OT methods for battlefield benefit), it will proceed for the foreseeable future.”
He provides, “That is why it’s essential to maintain bettering cyber defenses and (as highlighted within the DoD Cyber Technique highlights) disrupt adversaries’ efforts.”